SC EEPROM
Most of the information we have about the sc eeprom comes from graf_chokolo reverse engineering of the HV see Hypervisor Reverse Engineering
Here is where system flags, tokens and hashes are stored.
Right now most of the communication we have with the sc eeprom is through Linux using graf_chokolo ps3dm-utils and/or using his payloads.
See also Discussion page and Zer0Tolerance
SC EEPROM Info
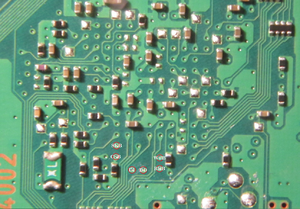
SC EEPROM from fat consoles is a custom/proprietary EEPROM chip that uses a special non standard commands to read/write from EEPROM. We are so lucky that Sony had exposed EEROM chip legs out of Syscon, so we have a physical access to it and we could attach devices like "Logic Analyzer", "Protocol Analyzer", "Custom made MCU boards" to capture traffic between console and Syscon EEPROM.
For FAT console Syscon EEPROM consists of: 0x4000 blocks, and every block is consists of 2 bytes of data. So the total EEPROM size is: 0x8000 byte length.
And since the pin-out of Syscon chip for Slim & Super Slim consoles is not known till now, we can not be sure if the Syscon EEPROM pins are exposed outside or not so we can access it like in FAT console without handling Syscon it self.
SC EEPROM Commands
FAT console's SC EEPROM used a standard SPI protocol with a proprietary commands as flow:
| Description | Command | Note |
|---|---|---|
| Unlock Command | 0xA3 0x00 0x00 | This command must be send first before write command. |
| Write Command | 0xA4 0xXX 0xXX | XX XX is a block id to be written (value 0x0000 to 0x3FFF), the maximum data to be written in one command cycle is 32 byte length (16 blocks). |
| Read Command | 0xA8 0xXX 0xXX | XX XX is a block id to be read (value 0x0000 to 0x3FFF), there is no maximum limit for read command so we can send it once with block id 0x00 0x00 then read the full EEPROM at once without sending read command again. |
| Check Status Command | 0xA9 0x00 0x00 0x00 | The response of this command is 0xFFFFFFFF if there is no error, or any other value if there is error happened or EEPROM still busy doing something. |
SC EEPROM dumps
- https://mega.co.nz/#!Bt8klAhQ!-t5YVetoL9gz6iZucpqQB9Vl9chCkbhFiMfqjbmotoc MD5:
B0E0551116B718A4921757B2B074693F - https://mega.co.nz/#!B51wWJYA!zg8O-vCvRBOgK5mpzTQ1H2hgBZmykglmbksB5w1Mlfg MD5:
3E0E73DACF7E10F2369624EA439C661B(partial: MD5:7E2BAD4DFDEE485494C8749B1C3E5676/ MD5:05D9ED4B545C709C9C4564F047028DE8) - https://mega.co.nz/#!t50DCIiL!RYLvjm35nmH3JVfhsGIXFWVHxmCr07ERsFBWhAOxD_Q MD5:
95DDFB21D65E38F20CD66517B67EAE7F - https://mega.co.nz/#!x4V0XBgJ!inxGYA5s8lfAF5Pe-naKCzTa1r5pY8Pn18js3D7QlnI
- https://mega.nz/#!iV0nGY4I!94ByAd-sourgK8_l_4s-6BX_V7iVOrysQd55bI0N6ws MD5:
1DB1CAA8E3D54256A59D08B6AF2B9BC5(Dumped by Syscon EEPROM Flasher done by me "Abkarino" using Arduino Mega).
- https://mega.nz/#!AwF1jIaB!5qei9JOCzisgUHARcjARCw0zvQENkkvtAdd_O0dRUfI DECR eeprom dump from lv2 um_manager, needs documentation.
different consoles, same initial 16 bytes. maybe key/iv?
Important Offsets
EEPROM Offset Table - Flags and Tokens
Here is the table of EEPROM offsets that can be accessed through Update Manager (3.15):
| Offset | Size | Description |
|---|---|---|
| 0x02F00 | 8 | Downgrade Minimum Version String |
| 0x02F08 | 0x10 | Downgrade Minimum Version Build + Date Build String |
| 0x02F20 | 8 | Target ID? (HV bible lists the Target ID as 85 Europe, not 83 Japan) |
| 0x02F28 | 0xD0 | Padding/undocumented
00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF xx xx xx xx xx FF FF xx xx xx xx xx xx xx xx xx xx xx xx xx 00 00 00 00 FF xx 00 xx xx FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF xx xx xx 00 00 xx xx xx xx xx FF FF FF xx xx xx FF FF FF xx 00 |
| 0x02FF8 | 1 | Factory Bit (0 = ?, 1 = reset, 2 = ?, 3 = (on retails)) |
| 0x02FF9 | 0x7 | Padding/undocumented
00 00 00 00 xx xx xx |
| Offset | Size | Description | |
|---|---|---|---|
| 0x48000 | 0x13 | (lv0 NVS region 0 start) | |
| 0 | 0x48000 | 0x13 | (lv0 NVS region 0) |
| 0x48012 | - | (lv0 NVS region 0 end) | |
| 0x48013 | 0x2A | QA Token ECDSA Signature (=> 3.60 firmwares) | |
| 0x48800 | 0x0C | (lv0 NVS region 1 start) | |
| 1 | 0x48801 | 0xFF | - hv log settings/infos? - |
| 0x48802 | 1 | ||
| 0x48804 | 4 | bootrom failure code | |
| 0x48808 | 4 | bootrom failure timestamp | |
| 0x4880B | - | (lv0 NVS region 1 end) | |
| 0x48C00 | 0x20 | (lv0 NVS region 2 start) | |
| 2 | 0x48C00 | 1 | load_image_in_rom flag (os_boot_order_flag) |
| 0x48C01 | 1 | (force standalone mode related) | |
| 0x48C02 | 1 | debug interface (select_net_device) | |
| 0x48C03 | 1 | sys.dbgcard.dgbe.index (select_dgbe_device) | |
| 0x48C05 | 1 | update_flag for CEB | |
| 0x48C06 | 1 | FSELF Control Flag / toggles release mode (fself_ctrl) | |
| 0x48C07 | 1 | Product Mode (UM allows to read this offset, it can be also written but only when already in product mode) | |
| 0x48C08 | 1 | (UNKNOWN ?debug?)) | |
| 0x48C0A | 1 | QA Flag | |
| 0x48C0B | 1 | mode_auth_flag / gx enable | |
| 0x48C0C | 1 | bootrom diagnostic mode and parameter | |
| 0x48C0D | 1 | ||
| 0x48C0F | 2 | ||
| 0x48C11 | 1 | bootrom trace level (0x00: fatal errors, 0x01: errors, 0x02: information messages, 0x03: debug messages) | |
| 0x48C12 | 1 | ||
| 0x48C13 | 1 | Device Type (flash_ext_format) | |
| 0x48C14 | ? | cellos_spu_configure | |
| 0x48C18 | 4 | System Language XRegistry.sys#Settings ( /setting/system/language ) | |
| 0x48C1C | 4 | VSH Target (seems it can be 0xFFFFFFFE, 0xFFFFFFFF, 0x00000001 default: 0x00000000 /maybe QA,Debug,Retail,Kiosk?) | |
| 0x48C1F | - | (lv0 NVS region 2 end) | |
| 0x48C22 | 0x03 | (lv0 NVS region 3 start) | |
| 3 | 0x48C22 | 1 | be nclk (be_nclck_flag1) |
| 0x48C23 | 1 | be ref clk (be_nclck_flag2) | |
| 0x48C24 | 1 | Bank #0 OS-Flag (ros0 if 0xFF else ros1) (os_bank_indicator) | |
| 0x48C24 | - | (lv0 NVS region 3 end) | |
| 0x48C25 | 1 | Bank #0 rvkprg-Flag | |
| 0x48C26 | 1 | Bank #0 rvkpkg-Flag | |
| 0x48C27 | 1 | Bank #1 OS-Flag | |
| 0x48C28 | 1 | Bank #1 rvkprg-Flag | |
| 0x48C29 | 1 | Bank #1 rvkpkg-Flag | |
| 0x48C30 | 0x0D | (lv0 NVS region 4 start) | |
| 4 | 0x48C30 | 1 | SPE number Usally 0x06, can be set to 0x07 to enable the 8 SPE (restrict_spu) |
| 0x48C31 | 4 | sata_param | |
| 0x48C35 | 8 | spr_tbuw_value (cellos_spu_configure) | |
| 0x48C3C | - | (lv0 NVS region 4 end) | |
| 0x48C40 | 0x10 | (lv0 NVS region 5 start) | |
| 5 | 0x48C42 | 1 | HDD Copy Mode |
| 0x48C43 | 4 | ||
| 0x48C47 | 1 | Analog Sunset Flag, will disable AACS video output without HDMI cable soon | |
| 0x48C50 | 0x10 | Debug Support Flag | |
| 0x48C60 | 1 | Update Status | |
| 0x48C61 | 1 | Recover Mode Flag | |
| 0x48C62 | 8 | boot param | |
| 0x48C6A | 2 | factory process completion % | |
| 0x48C4F | - | (lv0 NVS region 5 end) | |
| 0x48C80 | 0x10 | (lv0 NVS region 6 start) | |
| 6 | 0x48C80 | 8 | (rsx.rdcy.0) |
| 0x48C88 | 8 | (rsx.rdcy.1) | |
| 0x48C8F | - | (lv0 NVS region 6 end) | |
| 0x48C90 | 0x30 | (lv0 NVS region 7 start) | |
| 7 | 0x48C90 | 8 | (rsx.rdcy.2) |
| 0x48C98 | 8 | (rsx.rdcy.3) | |
| 0x48CA0 | 8 | (rsx.rdcy.4) | |
| 0x48CA8 | 8 | (rsx.rdcy.5) | |
| 0x48CB0 | 8 | (rsx.rdcy.6) / game_board_storage_read | |
| 0x48CB8 | 8 | (rsx.rdcy.7) / game_board_storage_read | |
| 0x48CBF | - | (lv0 NVS region 7 end) | |
| 0x48CCE | 1 | 0xFF / 0xFE / 0x00 (?) | |
| 0x48CCF | 1 | pme_user debug printf flag ( & 0x03 ) | |
| 0x48CF0 | 0x10 | (NVS region start) | |
| 0x48CF0 | 1 | ss.common.printf.enabled | |
| 0x48CF1 | |||
| 0x48CF2 | |||
| 0x48CF3 | |||
| 0x48CF4 | |||
| 0x48CF5 | |||
| 0x48CF6 | |||
| 0x48CF7 | |||
| 0x48CF8 | |||
| 0x48CF9 | |||
| 0x48CFA | |||
| 0x48CFB | |||
| 0x48CFC | |||
| 0x48CFD | |||
| 0x48CFE | |||
| 0x48CFF | |||
| 0x48CFF | - | (NVS region end) | |
| 0x48D00 | 0x0C | (lv0 NVS region 8 start) | |
| 8 | 0x48D00 | 4 | ip_addr (dgbe_config) |
| 0x48D04 | 4 | ip_netmask | |
| 0x48D08 | 4 | ip_gateway | |
| 0x48D0B | - | (lv0 NVS region 8 end) | |
| 0x48D20 | 0x08 | (lv0 NVS region 9 start) | |
| 9 | 0x48D20 | 8 | spider.gbe0.macaddr.0 (0xFFFFFFFFFFFFFFFF if unused/nonpresent)
|
| 0x48D27 | - | (lv0 NVS region 9 end) | |
| 0x48D28 | 0x18 | (lv0 NVS region B start) | |
| B | 0x48D28 | 8 | spider.gbe0.macaddr.1 (FFFFFFFFFFFFFFFF if unused/nonpresent)
|
| 0x48D30 | 8 | spider.gbe0.macaddr.2 (FFFFFFFFFFFFFFFF if unused/nonpresent)
| |
| 0x48D38 | 8 | spider.gbe0.macaddr.3 (FFFFFFFFFFFFFFFF if unused/nonpresent)
| |
| 0x48D3F | - | (lv0 NVS region B end) | |
| 0x48D3E | 0x50 | (lv0 NVS region A start) | |
| A | 0x48D3E | 0x50 | QA Token - UM doesn't allow access to this offset but SC Manager can read/write it (qa_token) |
| 0x48D8D | - | (lv0 NVS region A end) | |
| 0x48D8E | 0x50 | mode_auth_data (read/cleared by ss_sc_init_pu, checked by spu_mode_auth) | |
In a standard mostly untouched ps3 the common value for this flags is 0xFF wich means not active, anything else means active (e.g. 0xFE)
To change this to an active status you have to write 0x00 to turn on the flag
Debug support flag is tied to EID which is supposed to be hashed and saves in SC EEPROM
QA flag is tied to QA token that is also saved in this part of the SC EEPROM
QA Token ECDSA Signature is stored in 0x48013 offset (starting from 3.60 firmwares)
Undocumented config
There is an unknown syscon response of 0x100 bytes when using NVS service with such params: BlockID=1, Offset=0, Size=0.
0000h: FF 02 FF FE FF 02 FF FF 19 FB E1 16 00 00 00 00 ÿ.ÿþÿ.ÿÿ.ûá..... 0010h: 17 74 B8 54 00 00 E1 18 00 04 00 00 0C 03 00 00 .t¸T..á......... 0020h: 3C 02 02 00 00 00 00 10 00 00 00 00 55 55 55 55 <...........UUUU 0030h: 00 00 00 00 00 00 00 00 17 E0 C8 52 00 00 E2 18 .........àÈR..â. 0040h: 01 50 00 35 40 01 03 00 00 00 00 10 1D 30 00 B3 [email protected].³ 0050h: 00 07 01 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0060h: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿ 0070h: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿ 0080h: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿ 0090h: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿ 00A0h: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿ 00B0h: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿ 00C0h: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿ 00D0h: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿ 00E0h: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿ 00F0h: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿÿ
This is 0x48800 on EEPROM
cech-c (NO BD Drive): http://pastie.org/private/grl0dc0dxajisa36chgm7w
lv0 SC EEPROM usage
[*] lv0 NVS regions: # start_offset end_offset block size 0 0x00 0x12 0x48000 0x13 1 0x00 0x0B 0x48800 0x0C 2 0x00 0x1F 0x48C00 0x20 3 0x22 0x24 0x48C00 0x03 4 0x30 0x3C 0x48C00 0x0D 5 0x40 0x4F 0x48C00 0x10 6 0x80 0x8F 0x48C00 0x10 7 0x90 0xBF 0x48C00 0x30 8 0x00 0x0B 0x48D00 0x0C 9 0x20 0x27 0x48D00 0x08 A 0x3E 0x8D 0x48D00 0x50 B 0x28 0x3F 0x48D00 0x18 [*] Example region data (taken from region cache): 2: 01 FF 05 FF FF FF FF FF FF FF 00 FF FF FF FF FF FF FF FF FE FF FF FF FF 00 00 00 01 00 00 00 00 3: FF FF 00 4: 06 18 18 17 18 FF FF FF FF FF FF FF FF 5: FF FF 0D 02 0A 02 FF FF FF FF FF FF FF FF FF FF 9: FF FF FF FF FF FF FF FF [*] lv0 SC EEPROM usage: name addr size structure dgbe_config 0x48D00 0x0C [0x04 ip_addr, 0x04 ip_netmask, 0x04 ip_gateway] restrict_spu 0x48C30 0x01 [0x01 flag] sata_param 0x48C31 0x04 [0x04 flag] os_bank_indicator 0x48C24 0x01 [0x01 flag] cellos_spu_configure 0x48C33 0x04 [0x04 config] flash_ext_format 0x48C13 0x01 [0x01 flag] cellos_flags 0x48C0F 0x02 [0x02 flags] qaf_enable 0x48C0A 0x01 [0x01 flag] UNKNOWN (debug?) 0x48C08 0x01 [0x01 flag] fself_ctrl 0x48C06 0x01 [0x01 flag] select_dgbe_device 0x48C03 0x01 [0x01 index] os_boot_order_flag 0x48C00 0x01 [0x01 flag] qa_token 0x48D3E 0x50 [0x50 token] UNKNOWN 0x48804 0x04 [0x04 value] UNKNOWN 0x48D20 0x08 [0x08 value] rsx.rdcy.7 0x48CB8 0x08 [0x08 value] rsx.rdcy.6 0x48CB0 0x08 [0x08 value] rsx.rdcy.5 0x48CA8 0x08 [0x08 value] rsx.rdcy.4 0x48CA0 0x08 [0x08 value] rsx.rdcy.3 0x48C98 0x08 [0x08 value] rsx.rdcy.2 0x48C90 0x08 [0x08 value] rsx.rdcy.1 0x48C88 0x08 [0x08 value] rsx.rdcy.0 0x48C80 0x08 [0x08 value] be_nclck_flag2 0x48C23 0x01 [0x01 flag] be_nclck_flag1 0x48C22 0x01 [0x01 flag] select_net_device 0x48C02 0x01 [0x01 index] spr_tbuw_value 0x48C35 0x08 [0x08 value] bootrom_trace_level 0x48C11 0x01 [0x01 level]
System Data From EEPROM
Here is the list of possible EEPROM offsets:
| Index | SC EEPROM Offset | Size Of Data | Description |
|---|---|---|---|
| 0 | 0x48D20 | 6 | ? |
| 1 | 0x48D28 | 6 | ? |
| 2 | 0x48D30 | 6 | ? |
| 3 | 0x48D38 | 6 | ? |
| 4 | 0x48D00 | 4 | ? |
| 5 | 0x48D04 | 4 | ? |
| 6 | 0x48D08 | 4 | ? |
Dumpable EEPROM Offset - Block ID and Block Offset Mapping Table (NVS Service)
Right now we only have read access to some portions of the eeprom to have access to this regions DM needs to be patched, see section dumping eeprom
| EEPROM Offset | Block ID | Block Offset | Description | Physical Offset |
|---|---|---|---|---|
| 0x48000 - 0x480FF | 0x00 | 0x48000 - 0x480FF | ? | 0x7000 |
| 0x48800 - 0x488FF | 0x01 | 0x48800 - 0x488FF | Bluray Drive Area | 0x7100 |
| 0x48C00 - 0x48CFF | 0x02 | 0x48C00 - 0x48CFF | Contains flags and tokens/ see above | 0x7200 |
| 0x48D00 - 0x48DFF | 0x03 | 0x48D00 - 0x48DFF | System Data Region | 0x7300 |
| 0x2F00 - 0x2FFF | 0x10 | 0x2F00 - 0x2FFF | "Industry Area" aka OS Version Area | 0x2F00 |
| 0x3000 - 0x30FF | 0x20 | 0x3000 - 0x30FF | "CS Area" | 0x3000 |
| All other offsets | Invalid | Invalid | ? |
Dumpable only with HW flasher EEPROM Offsets - Full Mapping Table (NAND Only)
| Physical Offset | Description |
|---|---|
| 0x0-0xF | magic1? (static bytes) |
| 0x10-0x29F | eEID1? (probably encrypted) |
| 0x560-0x95F | Authenticated Data Region 0 |
| 0x960-0xD5F | Authenticated Data Region 1 |
| 0xD60-0x115F | Authenticated Data Region 2 |
| 0x1160-0x155F | Authenticated Data Region 3 |
| 0x1560-0x195F | Authenticated Data Region 4 |
| 0x1960-0x1D5F | Authenticated Data Region 5 |
| 0x1D60-0x215F | Authenticated Data Region 6 |
| 0x2160-0x255F | Authenticated Data Region 7 |
| 0x2700 - 0x270F | magic2? (static bytes) |
| 0x2800 - 0x2BFF | Syscon Patch Content Top-Half |
| 0x4400 - 0x4FFF OR 0x7400 - 0x7FFF | Syscon Patch Content Bottom-Half |
| All other offsets | Unknown |
Authenticated Data Regions Crypto Analysis
Tests
- http://i.imgur.com/A8g00bD.png <- aes 128 cbc with fixed key and incremented iv (by 1 each time)
- http://i.imgur.com/HZDWGSk.png <- results
- http://i.imgur.com/2mtrtdm.png region 0 encrypted vs http://i.imgur.com/7bSdQni.png decrypted
- http://i.imgur.com/FGJKkuz.png region 7 encrypted vs
http://i.imgur.com/7TSeHWK.png decrypted
Conclusion
- different key for a different authenticated region.
- sony uses either aes 128-cbc or aes 256-cbc (most likely 128-cbc)
- sony does this weird cbc crypto in which they only decrypt portions of 0x10 bytes of the region, then increment or decrement (most likely increment) iv, and then decrypt again. i've decided to call it ctr-cbc
- most likely the keys used are session keys.
- most likely the iv used starts with 00, then gets incremented by 1 for each 0x10 bytes
Acknowledgements
- Zer0Tolerance for the crypto findings
- flatz for his awesome syscon tool
Dumping your SC EEPROM
Linux
First you need graf_chokolo kernel ps3dm-utils and linux_hv_scripts.
If you are ready.
Patch DM using linux_hv_scripts
dmpatch.sh
Read the data from the region you want for example (see tables above)
ps3dm_scm /dev/ps3dmproxy 0x48000 0xFF
You can see some coolstuff that containing dumps
Hashes
Where exactly the hashes are stored is still a secret, it is said that those hashes are stored in SC EEPROM
To retrieve the information about the packages you have installed you can also use ps3d_utils
Linux
Installed Package info
ps3dm_um /dev/ps3dmproxy get_pkg_info TYPE
Examples
get_pkg_info 1 - Core OS package
0003004100000000
get_pkg_info 2 - Revoke List for program
0003004100000000
get_pkg_info 3 - Revoke list for package
0002003000000000
get_pkg_info 4
deadbeaffacebabe
get_pkg_info 5
deadbeaffacebabe
get_pkg_info 6 - Firmware Package
0003005000000000
You can find more information about this in Hypervisor Reverse Engineering
Hashes
What algorithm is used and what exactly is hashed is still unknown (seems that the content of files is hashed by the SHA-1).
ps3dm_scm /dev/ps3dmproxy get_region_data ID
These hashes are checked by lv1 to make sure that the data has not been altered through SC Manager: scm_get_region_data: get_result: ret[X]: 0x%x
Examples
region_data 0 - Core OS package
00 03 00 41 00 00 00 00 00 c3 eb 01 96 24 d0 1c 26 14 f3 1c a4 a2 ff ce 81 77 3a 4c f8 42 86 04 ee 34 bb db be 1c a7 51 e5 59 f1 95 61 07 a5 eb
region_data 1
ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff
region_data 2
ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff
region_data 3 //Revoke List for program?
00 03 00 41 00 00 00 00 80 41 f6 b8 f2 d5 30 60 59 35 49 d7 f0 3d 58 57 87 00 88 11 ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff
region_data 4
ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff
region_data 5 //Revoke List for package?
00 02 00 30 00 00 00 00 ba 6e 1c d5 5f 48 5b 8b 3f cc c8 60 75 ce f6 83 b2 20 dc f4 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
region_data 6
de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be
region_data 7
de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be
region_data 8 - BD Firmware Package
00 03 00 50 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
region_data 9
de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be
region_data 10
de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be
region_data 11
de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be
region_data 12
de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be
region_data 13
de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be
region_data 14
de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be
region_data 15
de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be de ad be af fa ce ba be
region_data 16 - 47?
Dumped data
Here is an example of data from syscon which stores VTRM block key, SRK/SRH, region data, etc.
0x0000: 00 00 00 03 C0 00 00 FF 00 00 00 00 00 00 00 00 ................
0x0010: 01 A2 F6 6C 26 54 1A 54 CE A3 F9 71 50 2B A8 20 ...l&T.T...qP+.
0x0020: 33 0E F4 5F 77 19 96 A6 7A 84 5D C9 AE B9 50 73 3.._w...z.]...Ps
0x0030: AE 45 5D 8E 6C BB 80 4D 7E C5 BF A4 AC 8E E1 E5 .E].l..M~.......
0x0040: 82 9B 0A 57 9A 40 D9 0C 00 00 00 00 00 00 00 00 ...W.@..........
0x0050: 7F 03 00 94 B4 7C B6 50 51 E5 84 30 4D 51 77 7C ?....|.PQ..0MQw|
0x0060: 7C 03 00 94 B4 7C B6 50 51 E5 84 30 4D 51 77 7C |....|.PQ..0MQw|
0x0070: 7D 03 00 94 B4 7C B6 50 51 E5 84 30 4D 51 77 7C }....|.PQ..0MQw|
0x0080: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ................
0x0090: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ................
0x00A0: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ................
0x00B0: 00 03 00 55 00 00 00 00 50 12 F0 AD 3A 4F 9F 1B ...U....P...:O..
0x00C0: F9 F1 E1 D3 64 85 D4 01 19 9D 76 9E 5C 33 8D FE ....d.....v.\3..
0x00D0: 39 75 10 9B 73 43 69 89 2B F6 EE 53 15 4A 3B 06 9u..sCi.+..S.J;.
0x00E0: 00 03 00 55 00 00 00 00 7B C9 65 97 CF 0D 20 4B ...U....{.e... K
0x00F0: BB 6A B1 B9 B0 71 83 27 79 6F 16 08 FF FF FF FF .j...q.'yo......
-------------------------------------------------------------------------
0x0100: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ................
0x0110: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ................
0x0120: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ................
0x0130: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ................
0x0140: 00 01 00 00 00 00 00 00 B0 64 53 92 7F 5E 29 47 .........dS.?^)G
0x0150: 9C BC 84 58 4A F2 ED 0B 50 E1 BE F3 FF FF FF FF ...XJ...P.......
0x0160: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ................
0x0170: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ................
0x0180: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ................
0x0190: FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF FF ................
0x01A0: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x01B0: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x01C0: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x01D0: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x01E0: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x01F0: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
-------------------------------------------------------------------------
0x0200: 00 03 00 50 00 00 00 00 00 00 00 00 00 00 00 00 ...P............
0x0210: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
0x0220: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
0x0230: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0240: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0250: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0260: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0270: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0280: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0290: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x02A0: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x02B0: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x02C0: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x02D0: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x02E0: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x02F0: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
-------------------------------------------------------------------------
0x0300: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0310: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0320: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0330: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0340: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0350: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0360: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0370: DE AD BE AF FA CE BA BE DE AD BE AF FA CE BA BE ................
0x0380: 42 03 00 94 B4 7C B6 50 51 E5 84 30 4D 51 77 7C B....|.PQ..0MQw|
0x0390: 43 03 00 94 B4 7C B6 50 51 E5 84 30 4D 51 77 7C C....|.PQ..0MQw|
0x03A0: 40 03 00 94 B4 7C B6 50 51 E5 84 30 4D 51 77 7C @....|.PQ..0MQw|
0x03B0: 41 03 00 94 B4 7C B6 50 51 E5 84 30 4D 51 77 7C A....|.PQ..0MQw|
0x03C0: 46 03 00 94 B4 7C B6 50 51 E5 84 30 4D 51 77 7C F....|.PQ..0MQw|
0x03D0: 47 03 00 94 B4 7C B6 50 51 E5 84 30 4D 51 77 7C G....|.PQ..0MQw|
0x03E0: 44 03 00 94 B4 7C B6 50 51 E5 84 30 4D 51 77 7C D....|.PQ..0MQw|
0x03F0: 45 03 00 94 B4 7C B6 50 51 E5 84 30 4D 51 77 7C E....|.PQ..0MQw|
More samples
Tokens
Here we will document the different types off tokens known in the PS3 All tokens are tied? encrypted? using EID0. They enable additional repository nodes.
List
| Token | Location | Size | SPU module | Description |
|---|---|---|---|---|
| qa_token | sc_eeprom - 0x48D3E | 0x50 | spu_token_processor.self | |
| user_token | ? | ? | spu_utoken_processor.self | Encrypted/Signed |
| token_seed | ? | ? | ? | This is used to create the token with EID0 |
Token Seed
?
Structure
This section has to be corrected, is only based on debug strings, we need to decrypt the tokens
Token Seed
?
QA Token
User Token
| Address | Size | Description |
|---|---|---|
| ? | ? | m_magic |
| ? | ? | m_format_version |
| ? | ? | m_size |
| ? | ? | m_capability |
| ? | ? | m_expire_date |
| ? | ? | m_idps? |
| ? | ? | m_attribute |
| ? | ? | m_digest |
For every atribute in the token
| Address | Size | Description |
|---|---|---|
| ? | ? | attr:m_type |
| ? | ? | attr:m_size |
| ? | ? | attr:m_data |
Dumping SC EEPROM - hardware way
| Warning |
|---|
| You can use this method at your own risk. Author is not responsible for any hardware damages and failures. |
Bus Pirate 3 Solderless method
You need
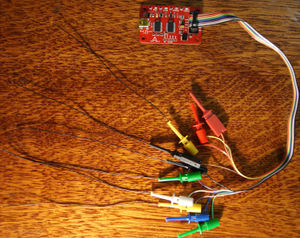
1) PS3 motherboard with BGA syscon chip (COK001, COK002, SEM001, DIA001, etc)
2) Bus Pirate v3.6 with connectors.
3) Wires (I used AWG32 150mm with tinned ends, see below)
4) PC with OS Windows7 (Should work on other windows systems, but not tested).
5) A sharp pencil.
6) Fingers ;)
Hardware Part
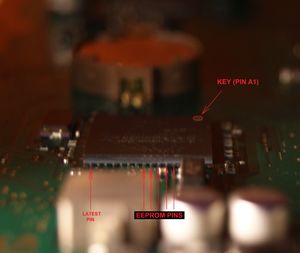
Find the syscon on your PS3 motherboard.
Look at the EEPROM Pins location and Draw serifs on the upper surface of the chip, strictly on these pins using pencil.
Draw the Pinout for convenience.
Connect Bus-Pirate and AWG32 wires using probe Kit
Connect Bus-Pirate to the EEPROM Pins using the folowing table:
| Bus Pirate pin | EEPROM pin |
|---|---|
| CLK | SKB |
| CS | CSB |
| MOSI | DI |
| MISO | DO |
| 3V3 | RBB |
| GND | Any Ground Point |
Use 1 finger to hold the wires. The wires should be well connected with the eeprom pins.
Connect Bus-Pirate to you PC with Windows7 by USB.
Software Part
Big thanks to Dasanko for the hard work and for the Syscon Flasher GUI Tool!!!
Download and Install the driver for Bus-Pirate.
Download link: http://www.ftdichip.com/Drivers/CDM/CDM%20v2.12.00%20WHQL%20Certified.exe
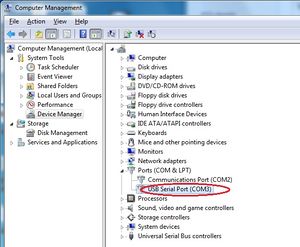
Open the Device Manager and find the port number of your USB Serial Port.
Download and Run Syscon Flasher.exe
Download link: https://mega.co.nz/#!clljxQgQ!vE93p35DJ9-FMKuxpev3zZvPBnxP_IQscPSXK9ocmH8
MD5=D59A8AA9E7BB1AEB753D7C6391CE17B1
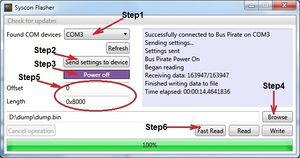
There are 6 simple steps to obtain the dump.
1) Select the correct USB Serial Port for Bus-Pirate.
2) Press "Send settings to device" button. If done correctly, then "Mode" Led on the Bus Pirate will be Green.
3) Press "Power on" button. If done correctly, then "VREG" Led on the Bus Pirate will be Red.
4) Press "Browse" button and specify location and file name for your syscon eeprom dump.
5) Specify Offset and Length. Offset=0 Length=0x8000 for full dump the eeprom.
6) Press "Fast Read" button and wait about 15sec.
Enjoy:
My dump, for example:
https://mega.co.nz/#!E1kHgSZJ!4e7TdNLdkQQzinwlnRO2KmaBd0GeBliHuHFe2tkmBgQ
Bus Pirate 3 method by: (Zer0Tolerance)
You need
1) PS3 motherboard. I am using DIA-001. may be we can dump it from another boards, but it is unknown yet.
2) Device that can work with SPI interface and send any commands. I am using a Bus Pirate v3.6 with connectors.
3) Soldering station.
4) Wires (see below).
5) Personal conputer with installed HxD, Putty (or other terminal supporting serial port connections, e.g.:Tera Term) , Notepad++
6) /dev/Hands ;)
Preparation
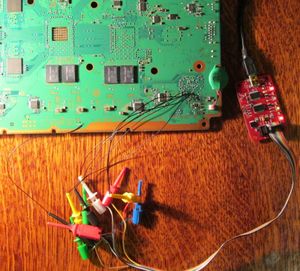
Find the test points on the motherboard using this picture.
All points are covered with varnish. You need to carefully remove the varnish to the copper and solder the wires to it.
Attach a Bus Pirate to the wires using the following table:
| Bus Pirate pin | Test Point |
|---|---|
| CLK | SKB |
| CS | CSB |
| MOSI | DI |
| MISO | DO |
| 3V3 | WCB, RBB |
| GND | Any Ground Point |
Make sure that the battery is attached to the motherboard.
Plug your Bus pirate to the USB port on your PC using mini_USB_to_USB cable. (I am using the cable from the ps3 gamepad)
It should be done like this, see the following picture:
Setup software
1) Install the driver for the Bus Pirate and setup your virtual COM port for it using following table:
| Parameter | Value |
|---|---|
| Bits per second | 115200 |
| Data bits | 8 |
| Parity | None |
| Stop bits | 1 |
| Flow control | None |
Open Putty and set it up:
session params:
connection type: Serial
Serial line: COM3 (choose your virtual COM port)
Speed (baud rate): 115200
Logging params:
Session logging: All session output
Log file name: click Browse button and specify your logfile, for example: C:\PS3\Logs\logfile.log
Now click Open button and setup mode for bus pirate using following commands:
| Command | Description |
|---|---|
| m | (mode) |
| 5 | (SPI) |
| 4 | (Set speed: 1MHz) |
| 2 | (Clock polarity: Idle high) |
| 1 | (Output clock edge: Idle to active |
| 1 | (Input sample phase: Middle *default) |
| 2 | (CS: /CS) |
| 2 | (Select output type: Normal (H=3.3V, L=GND)) |
Enable 3.3V: Just type: W (big leter) and press Enter.
Obtain the dump
Type: [0xa8 0x00 0x00 r:32768] and press Enter.
Wait until dumping process will be completed and close Putty.
Thats all. The dump must be into your logfile.log
You can use Notepad++ and Hex Editor like HxD to convert the dump to binary format.
Read Command is 0xA8 0xXX 0xXX, XX XX is a block id to be read, the full EEPROM is 32768 bytes lenght (0x8000), [r:] are syntax command of the Bus Pirate for start, read byte and end
Arduino Mega method by: (Abkarino)
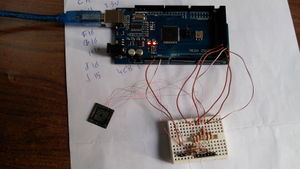
I had build my own Syscon EEPROM flasher based on open source hardware "Arduino Mega" and some resistors.
This flasher will allow you fully read/write to your Syscon EEPROM (FAT consoles only till now).
You need
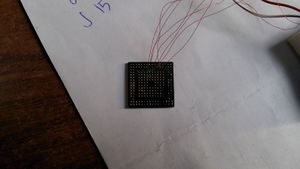
1) PS3 motherboard. I had used SEM-0001 board by desoldering Syscon chip form it but you can use, DIA-001 for example without desoldering Syscon chip since all eeprom pins had a test points in the board it self.
2) Arduino Mega or any Arduino board.
3) 6 x 3.6 KOHM resistors + 6 x 1.8 KOHM resistors (work together as a voltage dividers since Arduino IO logic is 5.0v and Syscon EEPROM IO Logic is 3.3v).
4) Soldering station.
5) Wires & Bread board (Optional).
6) Any PC that have terminal software like Putty, RealTerm and so on to access serial port, and any Hex Editor like HxD.
Preparation
Find the test points on the motherboard using this picture.
Or if you have a very good soldering skills and tools to desolder your SysCon then you can desolder your SysCon and solder your wires to it directly.
All points are covered with varnish. You need to carefully remove the varnish to the copper and solder the wires to it.
Attach a Arduino Mega to the wires using the following table:
| Arduino Mega pin | Test Point | Syscon Pin |
|---|---|---|
| SCL (52) | SKB | E16 |
| SS (53) | CSB | F16 |
| MOSI (51) | DI | G16 |
| MISO (50) | DO | H16 |
| WP (48) | WCB | J15 |
| RB (49) | RBB | J16 |
| VCC (3.3v) | Not needed if you used battery power | G11 |
| GND | Any Ground Point | C15 |
Make sure that the battery is attached to the motherboard if you will dump/flash SysCon EEPROM in board.
Wiring Diagram & Photos
Arduino Sketch Source Code
Here is my Arduino Mega sketch source code to allow you to read/write/erase PS3 Syscon EEPROM. http://pastie.org/10004682#8,19