SIG File Format: Difference between revisions
(This is a test, hello Discord!) |
|||
| (11 intermediate revisions by 6 users not shown) | |||
| Line 1: | Line 1: | ||
=Objects= | =Objects= | ||
Objects used by the .SIG files. | Objects used by the .SIG files. | ||
* | *CONSOLE | ||
** | **Windows command-line (cmd) | ||
*DIAGSERVICE | |||
**PinJig diagnose | |||
*EDIT | |||
**SIG/XLS Editor (Sakura Editor / Microsoft Office) | |||
*FILE | *FILE | ||
**A file operation, currently thought to be in the temp directory of the USB | **A file operation, currently thought to be in the temp directory of the USB | ||
* | *PIO | ||
**Unknown | **Contec GPIB Interface (to PinJig) | ||
*PKG CERTIFICATE | |||
**Unknown | |||
*PRINTER | |||
**Label Printer | |||
*RS232C <!-- PSP --> | |||
**misc. UART Port | |||
*PS/2 | *PS/2 | ||
**Likely from a barcode reader on COM1 with '''9600,7,2,0,50,0,0,0,0''' as settings. | **Likely from a barcode reader on COM1 with '''9600,7,2,0,50,0,0,0,0''' as settings. | ||
*PS3LV2DIAG | *PS3LV2DIAG | ||
**Functions in the LV2Diag | **Functions in the LV2Diag | ||
* | *PS3PICSY | ||
**Unknown | **Unknown, likely WWCS communications to a centralized server used at the factory or repair center. | ||
*PS3UART | |||
**Syscon UART | |||
*SKZPDM | |||
**Sony EMCS factory server | |||
*SMTP | |||
**Mail | |||
*TCP/IP/C | |||
**TCP client | |||
*TCP/IP/S | |||
**TCP server | |||
*TOOLKIT | |||
**ObjectiveSuites built-in | |||
=Functions= | =Functions= | ||
| Line 25: | Line 45: | ||
*for options, a HEX number | *for options, a HEX number | ||
*for options, two comma delimited values | *for options, two comma delimited values | ||
*for other arguments, ''file://temp:'' for a file located in | *for other arguments, ''file://temp:'' for a file located in the temp folder of the USB flash drive. | ||
*for other arguments, a string to be displayed | *for other arguments, a string to be displayed | ||
| Line 162: | Line 182: | ||
=Files leaked by an0n= | =Files leaked by an0n= | ||
Objective suites creates files in the temp folder inside the Objective Suites folder where the EXE is ran whenever it processes | Objective suites creates files in the temp folder inside the Objective Suites folder where the EXE is ran whenever it processes the commands in a sig file. This section attempts to unravel what these files are. | ||
==auth_0.txt== | ==auth_0.txt== | ||
| Line 180: | Line 200: | ||
This file is (probably) the NIC that authenticated (it '''''IS''''' one of the NICS in retrieved in earlier lines of the SIG file) and another MAC address, of which the source is unknown at this time. | This file is (probably) the NIC that authenticated (it '''''IS''''' one of the NICS in retrieved in earlier lines of the SIG file) and another MAC address, of which the source is unknown at this time. | ||
== | ==request_idps_in.txt== | ||
''(the one one after this is all you have left math of CEX-DEX)'' | ''(the one one after this is all you have left math of CEX-DEX)'' | ||
| Line 189: | Line 209: | ||
This data is sent to Sony's servers to process. The product is sent back to Objective suites. | This data is sent to Sony's servers to process. The product is sent back to Objective suites. | ||
== | (Kiban :from Japanese 機番 = machine number) | ||
==request_idps.txt== | |||
'''This is the file needed for the SET-IDPS portion of the original CEX-DEX leak.''' It is: | |||
pd_label_bin_ascii.txt + [the result of the call to sony for request_idps_in.txt] | |||
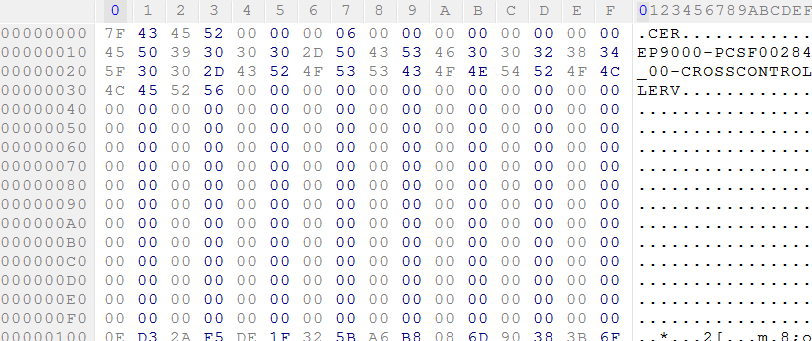
=CERTIFICATE= | |||
[[File:Pkgsig.JPG]] | |||
==Structure== | |||
{| class="wikitable sortable" | |||
|- | |||
! Offset !! Length !! Value !! Note | |||
|- | |||
| 0x0 || 0x4 || '.CER' || magic | |||
|- | |||
| 0x4 || 0x4 || 0x00000006 || type? | |||
|- | |||
| 0x8 || 0x4 || 0 || | |||
|- | |||
| 0xC || 0x4 || 0 || | |||
|- | |||
| 0x10 || 0x30 || 'EP9000-PCSF00284_00-CROSSCONTROLLERV' || NP Content Id | |||
|- | |||
| 0x40 || 0xC0 || 0 || padding? | |||
|- | |||
| 0x100 || 0x100 || encrypted data || Password/Certificate PKG information? | |||
|} | |||
Cross Controller Game list: | |||
*Sly Cooper: Thieves in Time | |||
*Ultimate Marvel vs Capcom 3 | |||
*LittleBigPlanet 2 (extra edition or updates/DLC) | |||
*Guacamelee! | |||
{{File Formats}}<noinclude>[[Category:Main]]</noinclude> | |||
Latest revision as of 06:45, 23 March 2023
Objects[edit | edit source]
Objects used by the .SIG files.
- CONSOLE
- Windows command-line (cmd)
- DIAGSERVICE
- PinJig diagnose
- EDIT
- SIG/XLS Editor (Sakura Editor / Microsoft Office)
- FILE
- A file operation, currently thought to be in the temp directory of the USB
- PIO
- Contec GPIB Interface (to PinJig)
- PKG CERTIFICATE
- Unknown
- PRINTER
- Label Printer
- RS232C
- misc. UART Port
- PS/2
- Likely from a barcode reader on COM1 with 9600,7,2,0,50,0,0,0,0 as settings.
- PS3LV2DIAG
- Functions in the LV2Diag
- PS3PICSY
- Unknown, likely WWCS communications to a centralized server used at the factory or repair center.
- PS3UART
- Syscon UART
- SKZPDM
- Sony EMCS factory server
- SMTP
- TCP/IP/C
- TCP client
- TCP/IP/S
- TCP server
- TOOLKIT
- ObjectiveSuites built-in
Functions[edit | edit source]
Functions called by the .SIG files, arranged by the objects that are available. Functions can have one, more, or no arguments (s_data, s_delim, r_data, and r_delim) associated with it.
The following syntax items have been noticed:
- for options, temp:xxxx where xxxx is a file name in the temp folder of the USB flash drive
- for options, xml:xxxx where xxxx is the .SIG file name (XML data set name)
- for options, a HEX number
- for options, two comma delimited values
- for other arguments, file://temp: for a file located in the temp folder of the USB flash drive.
- for other arguments, a string to be displayed
TOOLKIT[edit | edit source]
- IsInit
- GetMacAddress
- MessageBox
- Exit
- GetDateTime
- CreateProcess
FILE[edit | edit source]
- Copy
- WriteRead
- Divide
- AsciiToBin
- MD5
- Length
- Erase
- AddC39M10W3
- Append
- GetProfileString
- AsciiToBinAscii
- Insert
- Operator
- Read
- HexToDec
PS3PICSY[edit | edit source]
- CheckWwcsAuthentication
- SetSessionId
- RequestWwcsJigData
- RequestLogisticsLabel
- RequestIdpsConfig
- RequestIdps
- RequestServerTime
- EntryWwcsLog
- RequestSetSerial
PS/2[edit | edit source]
- Read
PS3LV2DIAG[edit | edit source]
The functions available with this object will likely vary with the LV2DIAG used.
- Open
- WaitEvent
- ReadAscii
- WriteRead
- Close
- GetScErrLog
- UpdateSYSCON (Unleaked .SIG file in combination with a modified downgrade lv2diag)
EDIT[edit | edit source]
- Write
Tools useable for SIG files[edit | edit source]
ssleay32.dll patch[edit | edit source]
small ssleay32.dll patch for ObjectiveSuites (educational use only): http://www.sendspace.com/file/xoxehb
.SIG <> XLS[edit | edit source]
/*
* sigtool.c
*
* Copyright (C) an0nym0us
*
* This software is distributed under the terms of the GNU General Public
* License ("GPL") version 3, as published by the Free Software Foundation.
*
*/
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
int
main ( int argc, char *argv[] )
{
int i = 0 ;
FILE *src_file ;
FILE *dst_file ;
size_t buf_size = 0 ;
char *src ;
char *dst ;
if (argc != 3) {
fprintf(stderr, "usage: %s SOURCE_FILE.SIG DEST_FILE.XLS\n", argv[0]);
return -1;
}
src_file = fopen ( argv[1], "rb" ) ;
dst_file = fopen ( argv[2], "wb" ) ;
fseek ( src_file, 0L, SEEK_END ) ;
buf_size = ftell ( src_file ) ;
fseek ( src_file, 0L, SEEK_SET ) ;
src = malloc ( buf_size ) ;
dst = malloc ( buf_size ) ;
fread ( src, buf_size, 1, src_file ) ;
for ( i = 0; i < buf_size; i++ )
{
if ( src[i] >= 0x20 && src[i] <= 0x7e )
{
dst[i] = (char)0x9e - (char)src[i] ;
}
else
{
dst[i] = (char)src[i] ;
}
}
fwrite ( dst, buf_size, 1, dst_file ) ;
fclose ( src_file ) ;
fclose ( dst_file ) ;
free ( src ) ;
free ( dst ) ;
return ( 0 ) ;
}
source: http://pastie.org/private/s7bpqozymhn5bwxbjjqzq
unsig - SIG File De-/Recrypter[edit | edit source]
vote + download : http://psx-scene.com/forums/content/unsig-sig-file-decrypter-re-crypter-1771/
Files leaked by an0n[edit | edit source]
Objective suites creates files in the temp folder inside the Objective Suites folder where the EXE is ran whenever it processes the commands in a sig file. This section attempts to unravel what these files are.
auth_0.txt[edit | edit source]
auth_0.txt is the MAC of a NIC, the JIG PC's used at the repair centers may very well be dual homed. One NIC for PS3 Communication and one for external communication.
auth_1_.txt[edit | edit source]
auth_1.txt is the MAC of another NIC, the JIG PC's used at the repair centers may very well be dual homed. One NIC for PS3 Communication and one for external communication.
auth_01.txt[edit | edit source]
This file is simply:
auth_0.txt+auth_1.txt.
auth_10.txt[edit | edit source]
This file is simply:
auth_1.txt+auth_0.txt
auth_data.txt[edit | edit source]
This file is (probably) the NIC that authenticated (it IS one of the NICS in retrieved in earlier lines of the SIG file) and another MAC address, of which the source is unknown at this time.
request_idps_in.txt[edit | edit source]
(the one one after this is all you have left math of CEX-DEX)
This file is the following files concatenated together, in a tab delimited fashion:
pd_label.txt [tab] kiban_id.txt [tab] cid.txt [tab] ecid.txt [tab] idps_bbox_config_version.txt
This data is sent to Sony's servers to process. The product is sent back to Objective suites.
(Kiban :from Japanese 機番 = machine number)
request_idps.txt[edit | edit source]
This is the file needed for the SET-IDPS portion of the original CEX-DEX leak. It is:
pd_label_bin_ascii.txt + [the result of the call to sony for request_idps_in.txt]
CERTIFICATE[edit | edit source]
Structure[edit | edit source]
| Offset | Length | Value | Note |
|---|---|---|---|
| 0x0 | 0x4 | '.CER' | magic |
| 0x4 | 0x4 | 0x00000006 | type? |
| 0x8 | 0x4 | 0 | |
| 0xC | 0x4 | 0 | |
| 0x10 | 0x30 | 'EP9000-PCSF00284_00-CROSSCONTROLLERV' | NP Content Id |
| 0x40 | 0xC0 | 0 | padding? |
| 0x100 | 0x100 | encrypted data | Password/Certificate PKG information? |
Cross Controller Game list:
- Sly Cooper: Thieves in Time
- Ultimate Marvel vs Capcom 3
- LittleBigPlanet 2 (extra edition or updates/DLC)
- Guacamelee!
| |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||